Losing a Cell Phone is a Data Breach
Technology Consultant Russell Mickler of Vancouver, WA explains how losing a cell phone constitutes a potential data breach of unencrypted personal private information (PPI), and how small businesses need to respond to it.
Just Another Bad Day At The Office ...
The other day, a business associate told me a terrible story about losing his cell phone. He placed it on the roof of his car and it probably slid off and flew into the street. I was empathetic, but at the same time, I asked a critical question: "Did you perform any business on this phone?"
He answered that he did. I started asking a bit more. "Do you think any of the emails on your phone had names of people, personal private data like addresses and phone numbers, and account information with your institution?"
Sadly, his smile began to fade as he started to see where I was going with this line of reasoning. "My friend, you've got a data breach situation on your hands."
... Just Got a Whole Lot Worse
A data breach is a condition where unencrypted Personal Private Information (PPI) is suspected of being compromised, or, falls out of the control of its owner.
Most States have data breach laws that require reporting and disclosure of a data breach affecting their citizens. If you're a small business in Washington State, you're subject to RCW 19.255.010 governing data breach reporting to affected Washington citizens.
Unfortunately, there isn't a national data breach law: each and every state has their own standard which makes it very difficult to do business in this country. Example: if you're a Washington State company that does business with consumers in the State of Oregon, you're also governed by the ORS 646A.600 Oregon Consumer Identity Theft Protection Act. You'd have to respond to both states and their requirements equally.
Cell phones and other mobile devices (tablets, laptops, wearable computers) are unencrypted storage devices and might contain classified forms of PPI covered in the statute.
Unencrypted means that the data on the hard drive of the device isn't scrambled so that somebody can't access it, and sadly, adding a passcode or a fingerprint access to your cell does not encrypt the contents of the device.
Generally, in the State of Washington, if your mobile device contains email, notes, documents, or contact information that draws a line between a first and last name and:
- Social Security Number
- Driver's License Number or Washington Identification Card Number
- Account Number or Debit Card Number (in combination with any access password or PIN)
As a remedy, Washington State requires that you provide immediate notification to all affected parties in one of many possible forms for a breach consisting of less than 500,000 records:
- Written response
- Electronic notice ... "consistent with the provisions regarding electronic records and signatures set forth in 15 U.S.C. Sec. 7001"
And the law also specifically addresses the company's liability to consumer civil action to recover damages, exposing the company to lawsuit for things like identity theft. (And BTW: do note that these laws are a baseline, not covering anything federally recognized as classified forms of information like HIPAA, FERPA, or GLB.)
But Think Bigger Than the Law - Think About Your Social Obligation
The letter of the law is fairly specific, limited, and even provides exclusions for public information that could be obtained from governments and other sources.
But think about it. What if it was your PPI, your kid's PPI, the private checking account information of your company (although it didn't have a PIN or passphrase)? Wouldn't you want to know about the data breach so that you could take reasonable precautions to protect yourself?
It's kind of like the recent automaker testimonials before Congress lately. If you knew about something but didn't take action - didn't go above the letter of the law and embrace the spirit of the law - doesn't that violate social obligation? Ruin public trust? If any form of sensitive information fell out of your control, shouldn't you be notifying those affected, and keeping a record of your social response so that you can justify your transparency and defend yourself from civil litigation, or, embarrassing allegations of concealing your negligence?
What's worse: admitting to the problem, taking ownership of it, and being seen as a leader to accept responsibility and seek remedies? Or, being caught in a cover-up? Or have somebody somewhere else damaged because you didn't take reasonable steps to notify them of the breach?
Preventative Measures
Okay, how can we be proactive about this stuff? Make sure it doesn't happen in the first place?
- Have a Security Policy. A document from your executive management that describes what your company does during a data breach and how it will respond. This document will demonstrate management's awareness of their obligations as custodians of PPI.
- Have a Data Classification Policy. A document that classifies certain kinds of information within a company as being more or less sensitive, and dictates the kinds of controls and accessibility it should have. Example: this policy should state that SSN's, account numbers, WA Drivers License Numbers, and access codes are restricted forms of information, and should never be transmitted out of an encrypted state or to a mobile device. Ever. This document will demonstrate management's specific instructions on how to handle classified forms of PPI.
- Training. You must communicate your intentions and train your staff so that they understand the risks and obligations taken on by your firm, and, how data breach affects them as individuals.
- Audits. Periodically review the Technical Controls that enable these policies. Review cell phones of employees. Put in the necessary technical precautions to prevent
These are best-practice approaches to illustrating management's intention, recognizing their obligation, proactively identifying what forms of information should be classified and how they should be treated, training staff, and auditing compliance.
Without these instruments or practices, the company is at best a poor custodian and at worse negligent, seriously exposing their firm to civil action from consumers damaged by identity theft.
R
Shouldn't Technology Make Things Faster?
Russell Mickler, a computer consultant in Vancouver, Washington, explains that you should look for both financial and intuitive gains from your technology investments. Shouldn't investment in technology make your business processes faster, more accurate, and more reliable? Well ... shouldn't it?
Quantitative vs. Qualitative Returns
Over the last two weeks, I've described ways to earn quantitative, monetary returns from technology investments - through reducing expenses, containing expenses, and generating revenue. And hey, money's great (I'm not going to argue with money), but you know, sometimes, it's not all about the money.
In my classes, I like to tell my students that technology should also do three other important things - three things that aren't money and are more qualitative in nature - and, if your technology investments aren't doing these things, then listen: there's a whole heck of a problem. Something is really, really wrong, and needs to be corrected.
Speed, Accuracy, and Reliability
Shouldn't technology ... make things faster? I mean, really. If you spend a bunch of money on a new computer and if it slows your business process down, how is that helping?
While we're on the subject, shouldn't technology ... make things more accurate? That's what computers are for, right? Reduce error rates? If a ton of money is spent on system upgrades and the computer system spits out bad information (and leading to bad decision-making), how is that helping?
Finally, shouldn't technology ... be more reliable? System's up. System's down. Wibbly-wobbly, undependable, reset this, restart that, pound it until it's working, how does that help anyone?
These are qualitative metrics in the sense that, off-hand, they generally are more felt than measured. Now, you can break this stuff down and attempt to measure time, accuracy, and reliability to give yourself more concrete metrics, absolutely, but intuitively, we can sense if something is faster or slower, more or less accurate, or, generally unstable; our feelings and gut reactions are pretty useful when understanding technology return as well.
In fact, it's the intuitive reaction from staff that gives management's first impression of its return on technology spending.
The Problem of Confidence
If the solution isn't faster, more accurate, and more reliable, there'll be no confidence in the system; users may even develop work-arounds or "shadowsystems" to do something the first solution was supposed to do!
That stuff eventually leads to even more complexity, more processes out of control, more time, more cost, more inefficiency and more waste.
Technology investments should improve confidence in the information system and the business processes it supports, not weaken it, no?
If This Ain't Happening ...
... something is seriously wrong. The implementation went south. The design was bad. The configuration isn't quite right. When implementing technology solutions, management's expectations of their vendor or solutions provider should be clear - the technical solution should do at least one of the following quantitative things:
- Reduce Expenses
- Contain Expenses
- Generate Revenue
And at least one of the following qualitative things (hopefully all three):
- Improve Speed
- Improve Accuracy
- Improve Reliability
Think about it. If you're a small business owner, why would you invest in technology if it was more expensive, cost more than adding additional labor, or generate money? Why would you invest in technology if it slowed stuff down, made data useless, or was inherently unreliable? How could you have confidence in the solution if your provider couldn't demonstrate these aspects of your return to you?
Next time: the power of perception.
R
The Z-Curve: the Timing of Technology Spending
Russell Mickler, technology consultant for small businesses in Vancouver WA, and Portland, OR, talks about how understanding the Z-Curve can help yield the highest rates of return on tech spend.
Does IT Spending Matter?
Nicholas Carr is one of the more controversial voices in my industry. Over over a decade, Mr. Carr has provided a contrarian view of IT spending and has even asked if IT spending really matters. His premise being that every technology eventually becomes ubiquitous and adopted by all, yielding businesses no competitive advantage. Crazy, eh? So his message begs us to ask, does tech spend really matter in the first place? If everyone eventually adopts technology at a ridiculously low cost an earns the same competitive differentiation from it's adoption, why are we interested in spending money on it ourselves?
Timing is Everything
Core to Mr. Carr's observations is understanding where your industry is along the Z-Curve for adopting new technology.
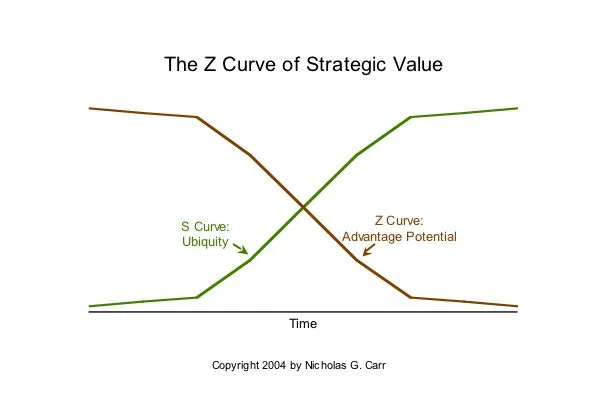
This is his Z-Curve of Strategic Value. Yes, it looks more like an X-Curve but put that aside for a moment. You'll notice the S-Curve (ubiquity curve) shows that, over time, there is a relatively limited number of early adopters who embrace the technology, but during that early adopting period, they earn the highest potential for competitive advantage because nobody else has it yet. That's the Z-Curve you're seeing there, and the gap is very wide.
Now, over time, as more and more people adopt the technology, the competitive advantage gained from reducing expenses, containing expenses, or generating revenue slides off. You have a smaller range of competitive advantage because more people are applying the technology. Its cost and complexity is coming down, and more and more companies are beginning to install it. Over time, the technology becomes cheap and ubiquitous: everyone can afford it, everybody can have it, and it's now just a common aspect of doing business. What this is telling us that there's a timing involved for investing in technology that's earning first-mover and follower advantages.
What's the Difference and Why Do I Care?
That's a great question and it matters from a strategic standpoint:
- If we're looking to earn the highest rate of return on our technology spending, we would want to make investments early on in the adoption curve for proprietary advantages;
- If we're looking to earn a modest rate of return on our technology spending without taking on unnecessary risks associated with first-movers, then we'd be making investments mid-stream in the diminished advantages stage of the curve;
- And if we're looking to just stay in the game and be relevant - to have the same technology that everyone else does in our industry and what our consumer expects us to have - then we'd be investing in the weak advantage stage of the curve.
Small business can take advantage of the Z-Curve by innovating with technology: adopting new technologies that are in the proprietary advantages segment of the curve and gain the highest rate of return. They can also plot where the weakest advantage may be earned from the technology dollar should they continue to wait for adoption. This kind of awareness is all about managing IT problems instead of just reacting to them. It's what I help my clients do every day.
R